
Soon after we learned that many HP laptops contain a keystroke logger, hundreds of thousands of Ransomware attacks pelted computers in over 150 countries.
Wait, whisper what’s Ransomware anyway? Well, it’s a sophisticated piece of software that blocks victims’ access to their files (much like Malware, except...the only way to regain access to the files is to pay a ransom.)
The WannaCry attack higher profile victims included 16 state run hospitals in the UK, a phone company in Spain (Telephonica), FedEx and LatAm Airlines.
WannaCry/WannaCrypt or Wana Decrypt0r displays a screen with the following message: 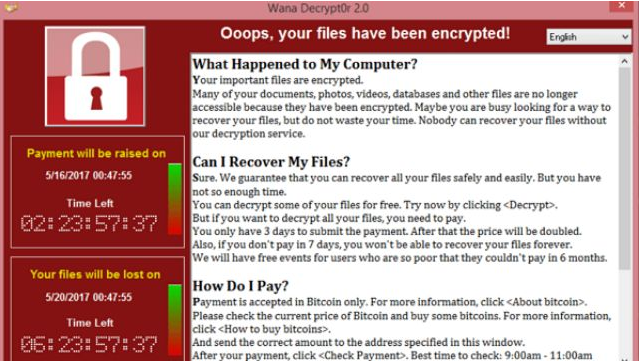
The bitcoin payment to decrypt files costs roughly $300 USD. Once purchased, it is to be sent to an online address. Bitcoin is often the currency used for ransomware because it is harder to trace than any other currency.
The danger with WannaCry, and all Malware, is that it can infect multiple devices on a network, taking down an entire business. WannaCry most nefariously exploits a vulnerability of the Windows XP operating system (not supported since 2014), but also attacks other Windows systems. Unbelieveably, NSA is the originator because it stockpiled this and other vulnerabilities in case it would ever need these tools to collect information These were leaked by the hacker group Shadow Brokers in April.
On Friday, it seemed as though WannaCry had been stopped by a tech blogger who unwittingly paused the scourge in its tracks. Unfortunately WannaCry is now back and brighter, without the Achilles heel of a kill switch.
If WannaCry is already on your machine, the best bet is to restore to factory settings and rely on backups. Paying could restore your files, but it might not (we don’t negotiate with terrorists!)
For tohers, please UPDATE YOUR SYSTEM! And take the usual precautions i.e. don’t open suspicious emails, don’t open attachments you weren’t expecting, don’t click on funny links and check the address bar in your browser to make sure it looks clean!
